Contents
※ Download: Ssh-keygen ubuntu
This may be overridden using the -a option. If you are happy with this, just press enter.

If you are using the standard port 22, you can ignore this tip. In public key based method you can log into remote hosts and server, and transfer files to them, without using your account passwords.

Contents - Wikipedia has a of how keys work. Multiple principals may be specified, separated by commas.
The type of key to be generated is specified with the -t option. If invoked without any arguments, ssh-keygen will generate an RSA key for use in SSH protocol 2 connections. See the MODULI GENERATION section for details. Normally each user wishing to use SSH with public key authentication runs this once to create the authentication key in , , or. Additionally, the system administrator may use this to generate host keys. Normally this program generates the key and asks for a file in which to store the private key. The program also asks for a passphrase. The passphrase may be empty to indicate no passphrase host keys must have an empty passphrase , or it may be a string of arbitrary length. A passphrase is similar to a password, except it can be a phrase with a series of words, punctuation, numbers, whitespace, or any string of characters you want. Good passphrases are 10-30 characters long, are not simple sentences or otherwise easily guessable English prose has only 1-2 bits of entropy per character, and provides very bad passphrases , and contain a mix of upper and lowercase letters, numbers, and non-alphanumeric characters. The passphrase can be changed later by using the -p option. There is no way to recover a lost passphrase. If the passphrase is lost or forgotten, a new key must be generated and the corresponding public key copied to other machines. For RSA1 keys, there is also a comment field in the key file that is only for convenience to the user to help identify the key. The comment can tell what the key is for, or whatever is useful. After a key is generated, instructions below detail where the keys should be placed to be activated. The options are as follows: -A For each of the key types rsa1, rsa, dsa and ecdsa for which host keys do not exist, generate the host keys with the default key file path, an empty passphrase, default bits for the key type, and default comment. This is used by system administration scripts to generate new host keys. For RSA keys, the minimum size is 768 bits and the default is 2048 bits. Generally, 2048 bits is considered sufficient. DSA keys must be exactly 1024 bits as specified by FIPS 186-2. For ECDSA keys, the -b flag determines they key length by selecting from one of three elliptic curve sizes: 256, 384 or 521 bits. Attempting to use bit lengths other than these three values for ECDSA keys will fail. This operation is only supported for RSA1 keys. The program will prompt for the file containing the private keys, for the passphrase if the key has one, and for the new comment. When used in combination with -s, this option indicates that a CA key resides in a PKCS 11 token see the CERTIFICATES section for details. This option allows exporting OpenSSH keys for use by other programs, including several commercial SSH implementations. This option is useful to find hashed host names or addresses and may also be used in conjunction with the -H option to print found keys in a hashed format. These primes must be screened for safety using the -T option before use. This replaces all hostnames and addresses with hashed representations within the specified file; the original content is moved to a file with a. These hashes may be used normally by ssh and sshd, but they do not reveal identifying information should the file's contents be disclosed. This option will not modify existing hashed hostnames and is therefore safe to use on files that mix hashed and non-hashed names. Please see the CERTIFICATES section for details. Please see the CERTIFICATES section for details. This option allows importing keys from other software, including several commercial SSH implementations. Private RSA1 keys are also supported. For RSA and DSA keys ssh-keygen tries to find the matching public key file and prints its fingerprint. If combined with -v, an ASCII art representation of the key is supplied with the fingerprint. Multiple principals may be specified, separated by commas. Please see the CERTIFICATES section for details. This option may be specified multiple times. Please see the CERTIFICATES section for details. The options that are valid for user certificates are: clear Clear all enabled permissions. This is useful for clearing the default set of permissions so permissions may be added individually. At present, no options are valid for host keys. The program will prompt for the file containing the private key, for the old passphrase, and twice for the new passphrase. This option is useful to delete hashed hosts see the -H option above. Please see the CERTIFICATES section for details. A validity interval may consist of a single time, indicating that the certificate is valid beginning now and expiring at that time, or may consist of two times separated by a colon to indicate an explicit time interval. The start time may be specified as a date in YYYYMMDD format, a time in YYYYMMDDHHMMSS format or a relative time to the current time consisting of a minus sign followed by a relative time in the format described in the TIME FORMATS section of 5. The end time may be specified as a YYYYMMDD date, a YYYYMMDDHHMMSS time or a relative time starting with a plus character. Causes ssh-keygen to print debugging messages about its progress. This is helpful for debugging moduli generation. Multiple -v options increase the verbosity. The maximum is 3. The default serial number is zero. MODULI GENERATION ssh-keygen may be used to generate groups for the Diffie-Hellman Group Exchange DH-GEX protocol. Generating these groups is a two-step process: first, candidate primes are generated using a fast, but memory intensive process. These candidate primes are then tested for suitability a CPU-intensive process. Generation of primes is performed using the -G option. The desired length of the primes may be specified by the -b option. For example: ssh-keygen -G moduli-2048. This may be overridden using the -S option, which specifies a different start point in hex. Once a set of candidates have been generated, they must be tested for suitability. This may be performed using the -T option. In this mode ssh-keygen will read candidates from standard input or a file specified using the -f option. For example: ssh-keygen -T moduli-2048 -f moduli-2048. This may be overridden using the -a option. The DH generator value will be chosen automatically for the prime under consideration. If a specific generator is desired, it may be requested using the -W option. Valid generator values are 2, 3, and 5. Screened DH groups may be installed in. It is important that this file contains moduli of a range of bit lengths and that both ends of a connection share common moduli. CERTIFICATES ssh-keygen supports signing of keys to produce certificates that may be used for user or host authentication. Certificates consist of a public key, some identity information, zero or more principal user or host names and a set of options that are signed by a Certification Authority CA key. Note that OpenSSH certificates are a different, and much simpler, format to the X. User certificates authenticate users to servers, whereas host certificates authenticate server hosts to users. By default, generated certificates are valid for all users or hosts. A certificate option may disable features of the SSH session, may be valid only when presented from particular source addresses or may force the use of a specific command. For a list of valid certificate options, see the documentation for the -O option above. Finally, certificates may be defined with a validity lifetime. The -V option allows specification of certificate start and end times. A certificate that is presented at a time outside this range will not be considered valid. By default, certificates have a maximum validity interval. For certificates to be used for user or host authentication, the CA public key must be trusted by 8 or 1. Please refer to those manual pages for details. FILES Contains the protocol version 1 RSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify a passphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 3DES. This file is not automatically accessed by ssh-keygen but it is offered as the default file for the private key. Contains the protocol version 1 RSA public key for authentication. The contents of this file should be added to on all machines where the user wishes to log in using RSA authentication. There is no need to keep the contents of this file secret. Contains the protocol version 2 DSA, ECDSA or RSA authentication identity of the user. This file should not be readable by anyone but the user. It is possible to specify a passphrase when generating the key; that passphrase will be used to encrypt the private part of this file using 128-bit AES. This file is not automatically accessed by ssh-keygen but it is offered as the default file for the private key. Contains the protocol version 2 DSA, ECDSA or RSA public key for authentication. The contents of this file should be added to on all machines where the user wishes to log in using public key authentication. There is no need to keep the contents of this file secret. Contains Diffie-Hellman groups used for DH-GEX. The file format is described in 5. SEE ALSO 1 , 1 , 1 , 1 , 5 , 8 The Secure Shell SSH Public Key File Format, RFC 4716, 2006. AUTHORS OpenSSH is a derivative of the original and free ssh 1. Aaron Campbell, Bob Beck, Markus Friedl, Niels Provos, Theo de Raadt and Dug Song removed many bugs, re-added newer features and created OpenSSH. Markus Friedl contributed the support for SSH protocol versions 1.
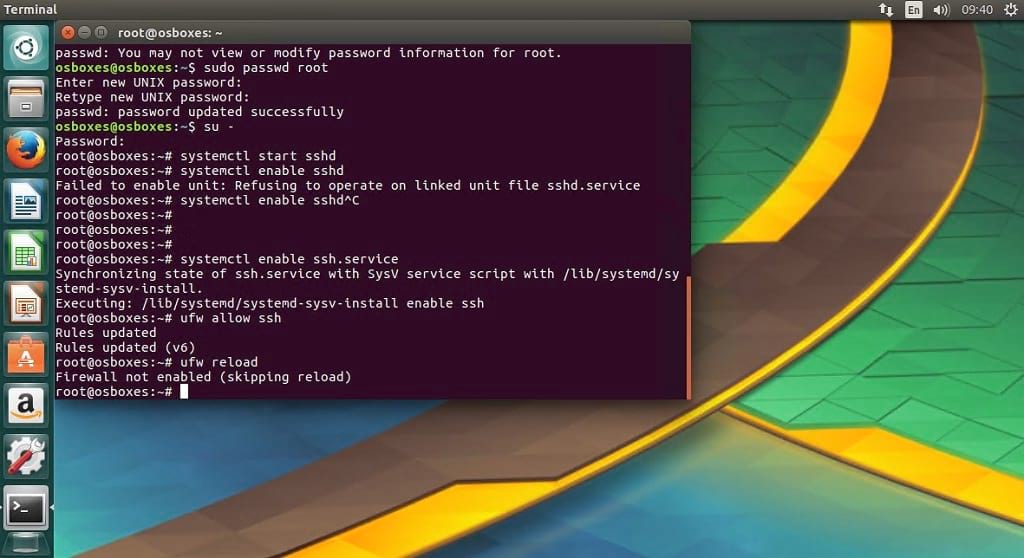
In public key based method you can log into remote hosts and server, and transfer files to them, without using your account passwords. SSH, the secure shell, is often used to access remote Linux systems. See the KEY REVOCATION LISTS section for details. Set up SSH server on Ubuntu 16. Different SSH programs generate public keys in different ways, but they all ssh-keygen ubuntu public keys in a similar format: Key-Based SSH Logins Key-based authentication is the most secure of several modes of authentication usable with OpenSSH, such as plain password and Kerberos tickets. If the passphrase is lost or forgotten, a new key must be generated and the corresponding public key copied to other machines. AUTHORS OpenSSH is a derivative of the ssh-keygen ubuntu and free ssh 1. MODULI GENERATION ssh-keygen may be used to generate groups for the Diffie-Hellman Group Exchange DH-GEX protocol. This is very useful as it adds an extra level of authentication and also works as a great protection against people trying to guess your passwords!.



